We want to be able to collect IntelliTrace information from our running app and also use remote desktop to connect to the IIS and look around(probably debugging).
1. Create certificate
1.1 Right-click the cloud project (marked in red) and select “Configure remote desktop”.
1.2 In the drop down list of certificates, choose <create> at the bottom.
1.3. Follow the instructions, you can set it up with default values.
1.4 When done. Choose the certificate and click “Copy to File…” as seen in the left of the picture above.
1.5. Save the file with any name you want.
Now we will save it to local storage to be able to import it to our solution through the azure configuration manager in step 3.
2. Save certificate to local storage
Now we need to attach it to our local certificate storage to be able to reach it from our confiuguration manager in visual studio. Microsoft provides the following steps for doing this:
http://support.microsoft.com/kb/232137
In order to view the Certificates store on the local computer, perform the following steps:
Now that you have access to the Certificates snap-in, you can import the server certificate into you computer's certificate store by following these steps:
- Click Start, and then click Run.
- Type "MMC.EXE" (without the quotation marks) and click OK.
- Click Console in the new MMC you created, and then click Add/Remove Snap-in.
- In the new window, click Add.
- Highlight the Certificates snap-in, and then click Add.
- Choose the Computer option and click Next.
- Select Local Computer on the next screen, and then click OK.
- Click Close , and then click OK.
- You have now added the Certificates snap-in, which will allow you to work with any certificates in your computer's certificate store. You may want to save this MMC for later use.
Now that you have the certificate backup imported into the certificate store, you can enable Internet Information Services 5.0 to use that certificate (and the corresponding private key). To do this, perform the following steps:
- Open the Certificates (Local Computer) snap-in and navigate to Personal, and then Certificates.
Note: Certificates may not be listed. If it is not, that is because there are no certificates installed.- Right-click Certificates (or Personal if that option does not exist.)
- Choose All Tasks, and then click Import.
- When the wizard starts, click Next. Browse to the PFX file you created containing your server certificate and private key. Click Next.
- Enter the password you gave the PFX file when you created it. Be sure the Mark the key as exportable option is selected if you want to be able to export the key pair again from this computer. As an added security measure, you may want to leave this option unchecked to ensure that no one can make a backup of your private key.
- Click Next, and then choose the Certificate Store you want to save the certificate to. You should select Personal because it is a Web server certificate. If you included the certificates in the certification hierarchy, it will also be added to this store.
- Click Next. You should see a summary of screen showing what the wizard is about to do. If this information is correct, click Finish.
- You will now see the server certificate for your Web server in the list of Personal Certificates. It will be denoted by the common name of the server (found in the subject section of the certificate).
You should now have an SSL/TLS-enabled Web server. Be sure to protect your PFX files from any unwanted personnel.
- Open the Internet Services Manager (under Administrative Tools) and navigate to the Web site you want to enable secure communications (SSL/TLS) on.
- Right-click on the site and click Properties.
- You should now see the properties screen for the Web site. Click the Directory Security tab.
- Under the Secure Communications section, click Server Certificate.
- This will start the Web Site Certificate Wizard. Click Next.
- Choose the Assign an existing certificate option and click Next.
- You will now see a screen showing that contents of your computer's personal certificate store. Highlight your Web server certificate (denoted by the common name), and then click Next.
- You will now see a summary screen showing you all the details about the certificate you are installing. Be sure that this information is correct or you may have problems using SSL or TLS in HTTP communications.
- Click Next, and then click OK to exit the wizard.
Image of a typical MMC.EXE with the certificates up.
3. Import the certificate to you visual studio project.
3.1 Now right click your equivalent to the MvcWebRole1 (as seen in the first picture under the red oval) and choose properties.
3.2 Choose Certificates. Right click the ellipsis to the right of the “thumbprint” and you should be able to select your newly created certificate here. After selecting it- save the file.
4. Upload the certificate to your Azure subscription.
4.1 Go to the azure management portal, click the services menu icon to the left and choose the service. Click Upload in the bottom menu.
5. Connect to server.
Since I tried to use account settings(have to use another name) we have to set up a new name for the connection. No biggie.
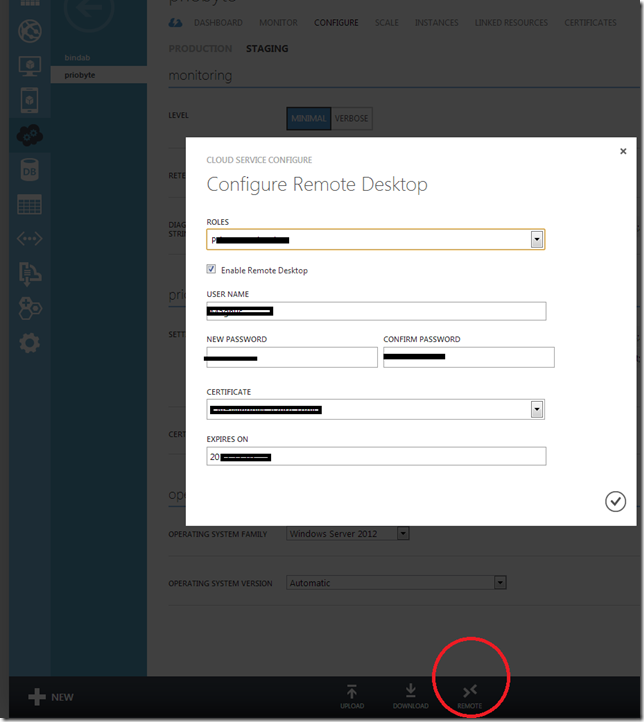
5.1 Go to azure management portal, select your service and in the bottom menu, choose “REMOTE”. This will display the configuration for remote connection. It will actually change your ServiceConfiguration.cscfg file. After you change It here it might be good to choose download and replace the one in your project. Set a name that is not your windows azure account name and not Administrator.
5.2 Goto visual studio, click Server Explorer. Choose as selected in the picture below and click “COnnect using remote desktop”.
5.2 You will now be able to log in with the name and password set up in step 5.1.
and voila! Windows server 2012, IIS and other nice stuff!
To do this one I’ve been using http://msdn.microsoft.com/en-us/library/windowsazure/ff683671.aspx where you can collect some of this information and additional one.






No comments:
Post a Comment